The third part of our playing with SELinux is about vncserver. Why vncserver? I want to show you creating new policies is not always necessary. Also I remember we had really hard time to make vncserver working :-).
First, we need to setup vncserver.
# yum install tigervnc-server# chcon -t bin_t `which /usr/bin/vncserver`Make your /etc/sysconfig/vncserver looking like
# cat /etc/sysconfig/vncserversVNCSERVERS="1:myusername"VNCSERVERARGS[2]="-geometry 800x600 -nolisten tcp -localhost"Add vnc password and start vncserver
# vncpasswd $myusername# service vncserver start# ps -eZ | grep vncsystem_u:system_r:initrc_t:s0 5558 ? 00:00:00 Xvncsystem_u:system_r:initrc_t:s0 5568 ? 00:00:00 vncconfigHow you know from the first part of blog
initrc_t -> bin_t -> initrc_tNow try to use the vncserver
# vncviewer localhost:1You might want to say: "It looks good, it works". But really? Try to run terminal in the vncviewer
# id -Zsystem_u:system_r:initrc_t:s0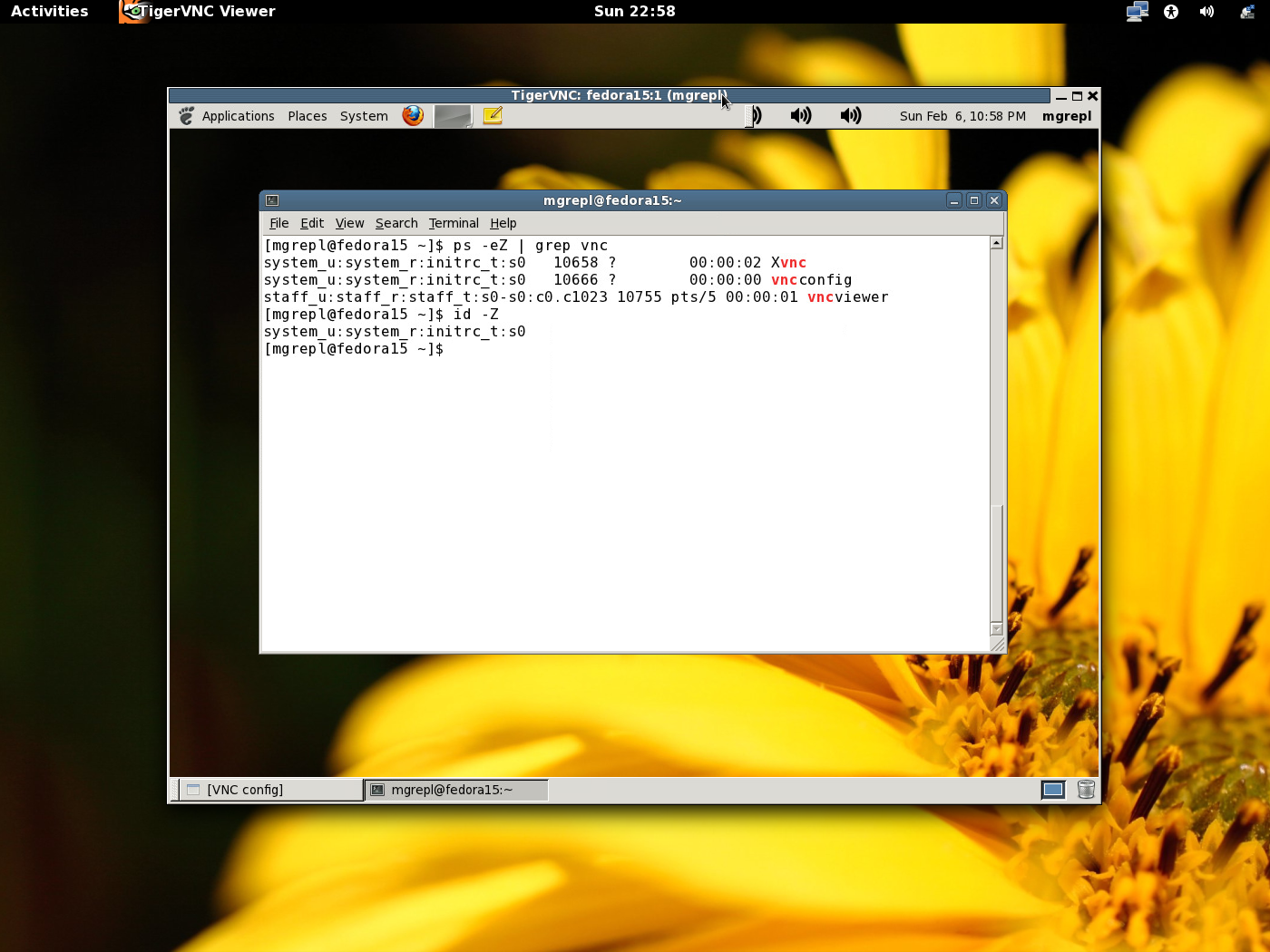
Bingo. You ended up with the wrong context. What does it mean? You could screw up your machine with wrong labels. For example:
# touch /tmp/test# ls -lZ /tmp/test-rw-rw-r--. mgrepl mgrepl system_u:object_r:initrc_tmp_t:s0 /tmp/testBut this is a wrong context for user's files in the /tmp directory. Should be:
# ls -lZ /tmp/test1-rw-rw-r--. mgrepl mgrepl staff_u:object_r:user_tmp_t:s0 /tmp/test1So how to fix it? By a new policy? It does not make sense in this case. The vncserver would end up as unconfined domain and still screw up our machines. We needed to find out a different solution.
... SELinux is all about labels.
Now run.
# restorecon -v `which vncserver`restorecon reset /usr/bin/vncserver context system_u:object_r:bin_t:s0->system_u:object_r:unconfined_exec_t:s0And yes, you are seeing our solution. We added the "unconfined_exec_t" label for the vncserver binary.
# service vncserver restart# ps -eZ | grep vncsystem_u:unconfined_r:unconfined_t:s0 6237 ? 00:00:00 Xvncsystem_u:unconfined_r:unconfined_t:s0 6245 ? 00:00:00 vncconfig# vncviewer localhost:1# id -Zsystem_u:unconfined_r:unconfined_t:s0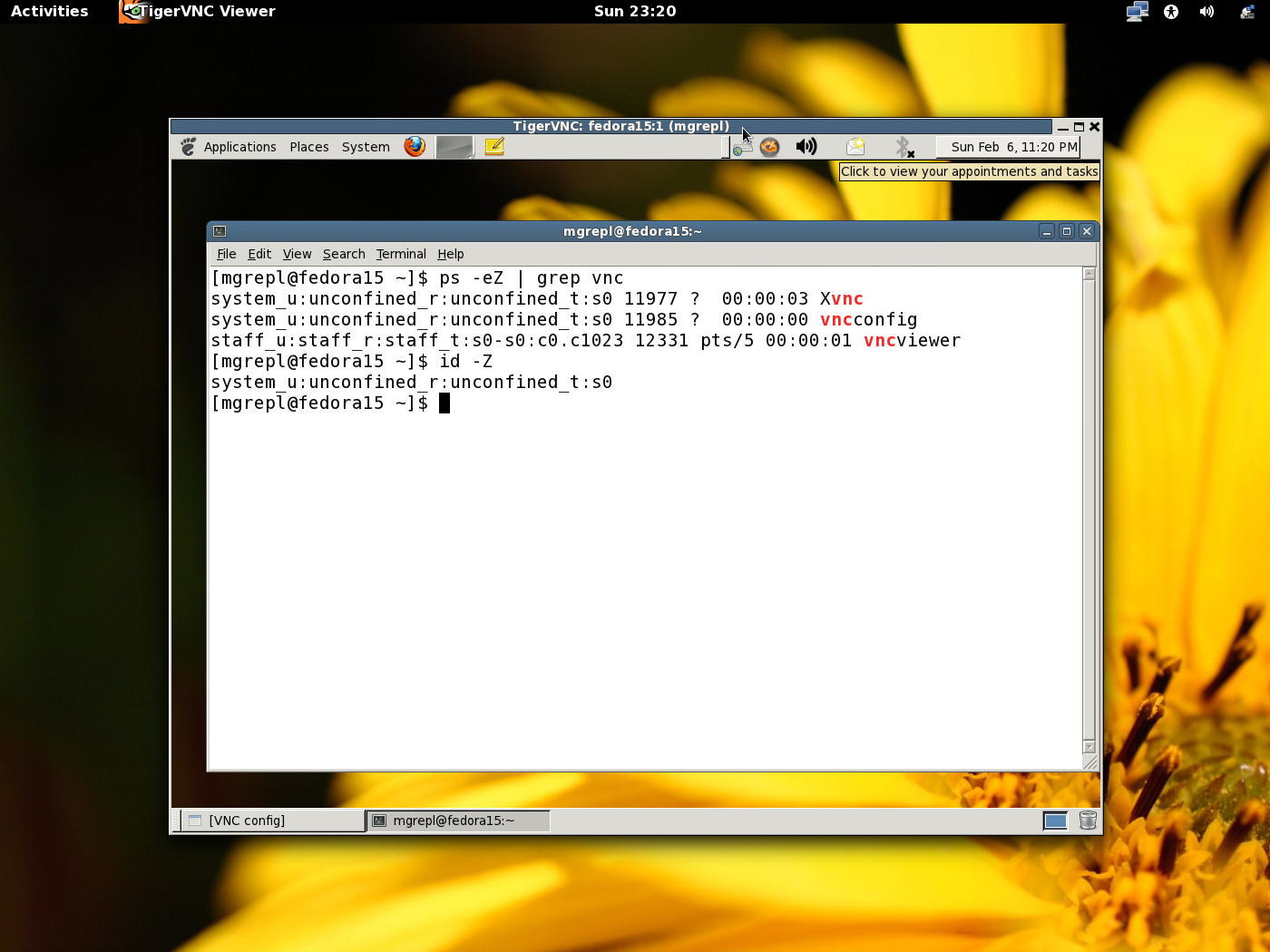
And we got the right context for unconfined SELinux user.